Cybersecurity in the Electrical Power and Energy System
The CyberSEAS project is a European Union funded collaborative project improving the cyber security of the European electrical power energy systems (EPES).
CyberSEAS (Cyber Securing Energy dAta Services) aims to improve the overall resilience of energy supply chains, protecting them from disruptions that exploit the enhanced interactions, the extended involvement models of stakeholders and consumers as channels for complex cyber-attacks, the presence of legacy systems and the increasing connectivity of energy infrastructures, data stores and services retailers.
CyberSEAS at a glance
SU-DS04-2018-2020
101020560
€ 10.067.121,25
€ 7.999.113,64
01/10/2021
30/09/2024
Research and methods
Project Objectives
CyberSEAS has 3 strategic objectives:
- Countering the cyber risks related to highest impact attacks against EPES;
- Protecting consumers against personal data breaches and attacks;
- Increasing the security of the Energy Common Data Space.
All three objectives are equally important, since cyber-criminals are shifting tactics to favour multi-stage attacks in which stealing sensitive data is a precondition for the real attack, and enables them to maximise damage and profits (while traditionally infrastructure cyber-attacks used to be direct attacks to the machinery and typically targeted control systems, not data). Threat actors, especially large ones such as nation states, also carry out complex attacks that leverage supply chain dependencies, and this trend continues to grow, as highlighted in the July 2020 analysis by the Atlantic Council. Likewise, with the transition to scenarios where users are proactively involved, prosumer data is becoming more and more sensitive.
Solutions
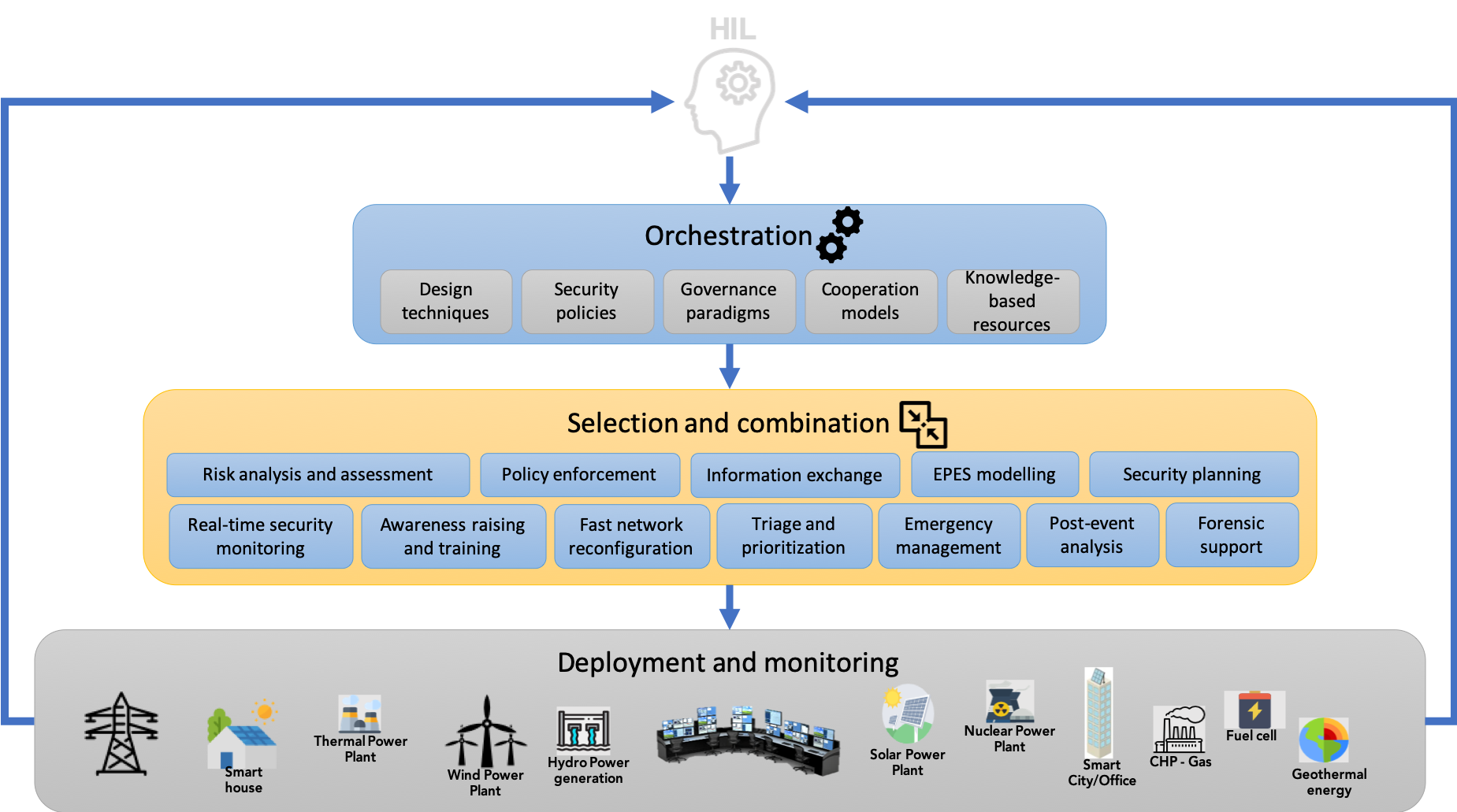
To achieve these objectives, CyberSEAS delivers an open and extendable ecosystem of 30 customisable security solutions providing effective support for key activities, and in particular:
- risk assessment;
- interaction with end devices;
- secure development and deployment;
- real-time security monitoring;
- skills improvement and awareness;
- certification, governance and cooperation.
CyberSEAS solutions are validated through experimental campaigns consisting of 100+ attack scenarios, tested in 3 labs before moving out to one of 6 piloting infrastructures across 6 European countries. Out of the 30 solutions, 20 will reach TRL8+ and 10 TRL7.
Team
CyberSEAS ’s management structure has been designed to ensure that project activities are properly coordinated, so that:
- the project reaches its objectives and fulfils partners’ individual expectations;
- quality assurance is guaranteed throughout project implementation;
- proper monitoring and self-assessment procedures are in place;
- security, ethical, legal, privacy, societal acceptance and training dimensions are taken into account.
The project is managed at different levels with management and support committees.

in industry (FP7 project CYSPA). His research team is now working on social engineering topic, by coordinating the creation of a Social-Driven Vulnerability Assessment framework (H2020 project DOGANA) and contributing to a phishing detection service (EIT project WAFFLE). He is coordinating two H2020 projects: COMPACT, to improve the resilience of Local Public Administrations against cyberattacks, and HERMENEUT,
to assess cyber risks on intangible assets of organizations. Projects: DILIGENT (Grid Computing, Digital Libraries), D4Science (Grid Computing, Digital Libraries), GriFin (Grid Computing, Finance), EchoGRID (Grid Computing, Industry, Telco), SEMIRAMIS (Security, Cross Border Information Exchanges), CYSPA (Cyber Risks, Industry), ACDC
(Botnets, Cyber Threat Intelligence), DOGANA (Social Engineering, Risk Assessment), WAFFLE (Phishing), COMPACT (Basic Cyber Threats, Public Administrations), HERMENEUT (Cyber Risks, Cyber Crime).

Mr. Luigi Romano (male). He is a Full Professor at the Department of Engineering of the university of Naples “Parthenope”. He is an expert in system security and dependability. In FP7, he was the Technical Coordinator/Principal Investigator of the INTERSECTION, INSPIRE, INSPIRE INCO, MASSIF, and SAWSOC projects. He is a member of the European Network and Information Security Agency expert group on Priorities of Research On Current and Emerging Network Technologies (PROCENT). He is the Chair of the “Cyber Security” Working Group within the context of the SERIT initiative (SERIT, “Security Research in ITaly” is the technological platform for national security jointly promoted by CNR and Finmeccanica). He is the technical coordinator of KONFIDO project and will be the technical coordinator of CyberSEAS.


He is also President of the Slovenian Association of Corporate Security and currently serves as the Chairman of the international association “SE Europe Corporate Security Association” (SECSA).
He worked as a Slovenian representative in the framework of NATO in the field of intelligence standardization matters in “Joint Intelligence Working Group at the period 2002-2008. He served as an Adviser for Counter Terrorism to the CHOD of Slovenian Armed Forces at the period 2002-2010. He was also member of the Government Coordination Group to coordinate the preparations for critical infrastructure protection for more than 10 years and was representative of the Slovenian Armed Forces in the working body for transnational threats inside the National Security Council (NSC) primarily concern for Counter terrorism activities.
He is national representative in EU RANNET (Radicalization Awareness Network).
Related project
The list of CyberSEAS-related projects and members of the Cybersecurity Innovation Cluster for EPES can be found here
































